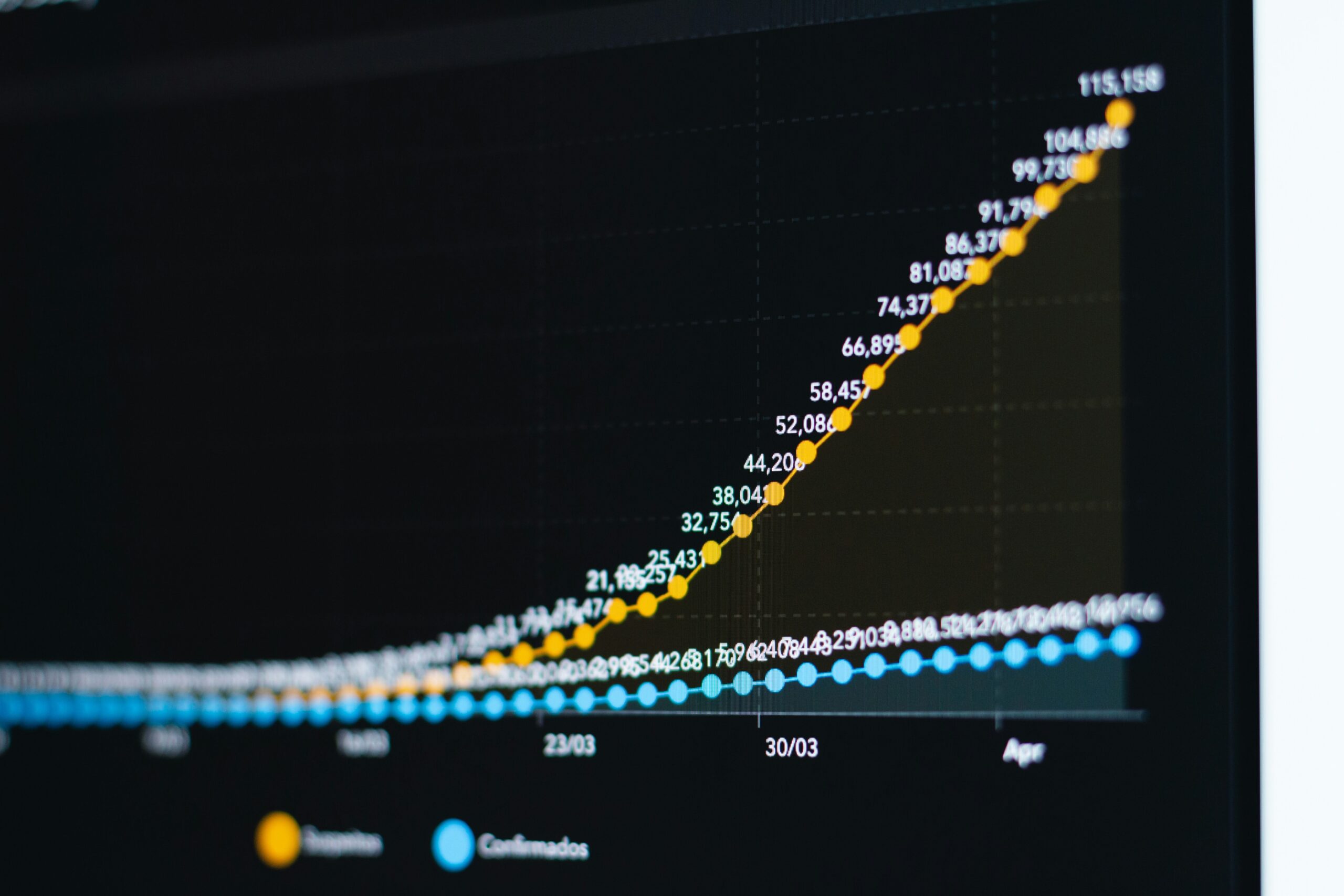
Ever clicked on a link in an email that seemed legit, only to realize seconds later that you might have just handed over your passwords to a cybercriminal? You’re not alone. According to Verizon’s 2023 Data Breach Investigations Report, phishing attacks accounted for 46% of all breaches. Yeah, they’re THAT common. And here’s the kicker—most people don’t even know they’ve fallen prey until it’s too late.
In this guide, we’ll tackle the nitty-gritty of email phishing protection. You’ll learn why these sneaky scams are so effective, how to recognize them (even when they feel “chef’s kiss” authentic), and actionable steps to safeguard yourself—and your data—from falling victim. Spoiler alert: It involves more than just ignoring suspicious emails!
Table of Contents
- Key Takeaways
- The Problem with Phishing
- Step-by-Step Guide to Email Phishing Protection
- Email Phishing Best Practices: What Actually Works?
- Real-World Examples of Phishing Success Stories (and Failures)
- Frequently Asked Questions About Email Phishing
- Conclusion
Key Takeaways
- Email phishing remains one of the top cybersecurity threats across industries.
- Phishing relies heavily on psychological manipulation, making traditional tech defenses incomplete without human training.
- Using multi-factor authentication (MFA) can reduce breach risks by up to 99.9%.
- Avoid generic advice—tailor phishing protection strategies to your specific organization or personal habits.
- Regularly updated tools like DMARC protocols and AI-driven email filters play vital roles in combating phishing.
The Problem with Phishing: Why It Keeps Winning
I’ll admit it—I once fell for a phishing scam myself. A colleague spoofed our HR department’s email address back in the day, asking me to verify my tax documents via what looked like a totally legit Google Form. I opened it, typed in some personal info, and hit “submit.” Cue facepalm. Fortunately, no harm was done beyond some awkward apologies, but it taught me something critical:
Phishing isn’t about hacking computers; it’s about hacking trust.
Cybercriminals exploit our natural tendencies to trust familiar names, logos, and processes. Factor in modern techniques like domain spoofing, lookalike URLs, and highly personalized bait (yes, spear phishing), and you’ve got yourself a recipe for disaster.
Optimist You: “Surely, firewalls and antivirus software will save us, right?”
Grumpy Me: “Ugh, if only life were that easy.”
The Grump’s Rant Section:
Let me tell you what really grinds my gears: Organizations thinking phishing simulations are enough. Just because someone clicks less during fake tests doesn’t mean they’re immune—it means they’ve been trained to spot obvious traps. Real-world phishing is far sneakier than those staged emails pretending to come from the CEO.
Step-by-Step Guide to Email Phishing Protection
Alright, time to get practical. Here’s your step-by-step battle plan against email phishing attempts:
1. Enable Multi-Factor Authentication (MFA)
If there’s ONE thing you do after reading this, let it be turning on MFA for EVERY account possible. Even if credentials get stolen through phishing, MFA adds another layer hackers rarely bypass.
2. Deploy DMARC Policies
DMARC (Domain-based Message Authentication, Reporting, and Conformance) helps prevent domain spoofing—the backbone of many phishing schemes. By configuring SPF and DKIM records correctly, your legitimate emails stand out while fakes get blocked.
3. Train Your Team (or Yourself)
Remember the confessional fail story earlier? Well, don’t make the same mistake. Invest in regular security awareness training that includes live examples, quizzes, and scenario-based testing. Make sure participants understand both the technical and emotional aspects of phishing.
4. Filter Emails with AI-Powered Tools
Say goodbye to basic spam filters! Modern solutions use machine learning to detect subtle signs of phishing—like mismatched sender details or weird urgency cues—that conventional systems miss.
Email Phishing Best Practices: What Actually Works?
- Hover Before You Click: Always check links by hovering over them before clicking. Does the URL match what you expect?
- Don’t Fall for Urgency Tactics: Phishers love creating panic (“Your account will be suspended!”). Take a breath, then verify independently.
- Keep Software Updated: Vulnerabilities often lead to successful phishing exploits. Patch everything, always.
- Use Password Managers: These tools auto-fill login fields, reducing the chance of entering creds into fake sites.
Terrible Tip Alert: Some people suggest disabling JavaScript in browsers to stop certain phishing attacks. Sure, it might work—but good luck navigating today’s web without JavaScript. Skip this bad advice unless you want to live in the digital Stone Age.
Real-World Examples of Phishing Successes—and Lessons Learned
In 2016, Snapchat became infamous for accidentally leaking payroll data due to a convincing phishing email targeting its HR team. Lesson learned? No matter how big your brand, complacency invites disaster.
On the flip side, companies like Microsoft and Google now leverage advanced AI models to proactively flag suspicious activity. Their success proves that proactive defense beats reactive cleanup every time.
Frequently Asked Questions About Email Phishing
What Makes Email Phishing So Effective?
Simply put, humans are predictable creatures prone to trust. Add clever social engineering tactics, and voilà—you’ve got a near-perfect attack vector.
Are There Any Warning Signs I Can Look For?
Absolutely. Misspelled words, strange greetings (“Dear Customer” instead of your name), unexpected attachments, and urgent calls-to-action are all red flags.
Is Free Anti-Phishing Software Worth It?
While free options exist, they pale compared to enterprise-grade solutions. If protecting sensitive data matters to you, invest in premium tools.
Conclusion
Email phishing protection isn’t rocket science—but it does require vigilance, education, and smart technology. Whether you’re managing corporate networks or simply trying to keep Grandma’s bank account safe, these tactics form the foundation of robust cybersecurity hygiene.
So go ahead, share this article with friends, coworkers, or anyone who needs a wake-up call. Because knowledge, my friend, truly is power.
P.S. Stay safe online—it’s wild out there. 🐱💻 Like vintage dial-up tones, phishing scams may evolve, but staying sharp keeps you ahead of the game.


