“What keeps CISOs up at night? Hint: It’s not just coffee refills. Malware continues to evolve faster than ever. In fact, a recent report revealed that ransomware attacks surged by over 130% last year alone. Scary enough for you?” Welcome to the deep dive on Malware threat reports, where we explore cybersecurity challenges like never before.
This post will unpack everything from why malware is such a persistent problem to actionable steps for staying ahead of it. You’ll learn how to interpret Malware threat reports, mitigate risks, and even get some brutally honest advice along the way (spoiler: not all hacks are silver bullets).
Table of Contents
- The Growing Menace of Malware in Modern Data Management
- How to Decode Malware Threat Reports Without Losing Your Mind
- Best Practices to Combat Malware Threats
- Real-Life Examples That Prove Malware Is No Joke
- FAQ: Answering Your Burning Questions About Malware Threat Reports
Key Takeaways
- New strains of malware appear every day, making vigilance crucial.
- Misinterpreting malware threat reports can cost businesses millions.
- Automation tools and employee training are key defenses against cyberattacks.
The Growing Menace of Malware in Modern Data Management
Let me paint you a picture. Imagine waking up one morning to find your company’s sensitive data encrypted—and held hostage by an anonymous hacker demanding $500k in Bitcoin. Sounds straight out of a thriller movie, right?
Oh wait—it’s real. This exact scenario happened to Colonial Pipeline in 2021, causing widespread panic across the U.S. East Coast. The attack leveraged DarkSide ransomware, which exploits vulnerabilities faster than most teams can patch them. Cybercriminals aren’t slowing down; they’re speeding up.

“Optimist You: ‘We’ve got firewalls and antivirus software!’ Grumpy Me: ‘Yeah, but do those stop zero-day exploits? Exactly.'”
How to Decode Malware Threat Reports Without Losing Your Mind
Okay, confession time. I once skimmed through a malware threat report thinking it was another boring compliance document. Fast forward two weeks later—our system crashed because we missed a critical vulnerability warning buried in paragraph five. Lesson learned: Always read between the lines!
Here’s a breakdown of what these reports typically cover:
- Trends: What types of malware are trending globally? For instance, phishing-based Trojans have spiked in Q3 this year.
- Vulnerabilities: Which industries or platforms are most targeted?
- Actionable Insights: Recommendations tailored to specific use cases (e.g., “Patch Remote Desktop Protocol immediately”).

Best Practices to Combat Malware Threats
To keep malware at bay, adopt these battle-tested strategies. But first, here’s one truly awful tip—something I’d only recommend if desperate:
Terrible Tip #1: Disable all internet connections forever. Problem solved, right? …Right?
(Don’t actually try this.) Now onto the good stuff:
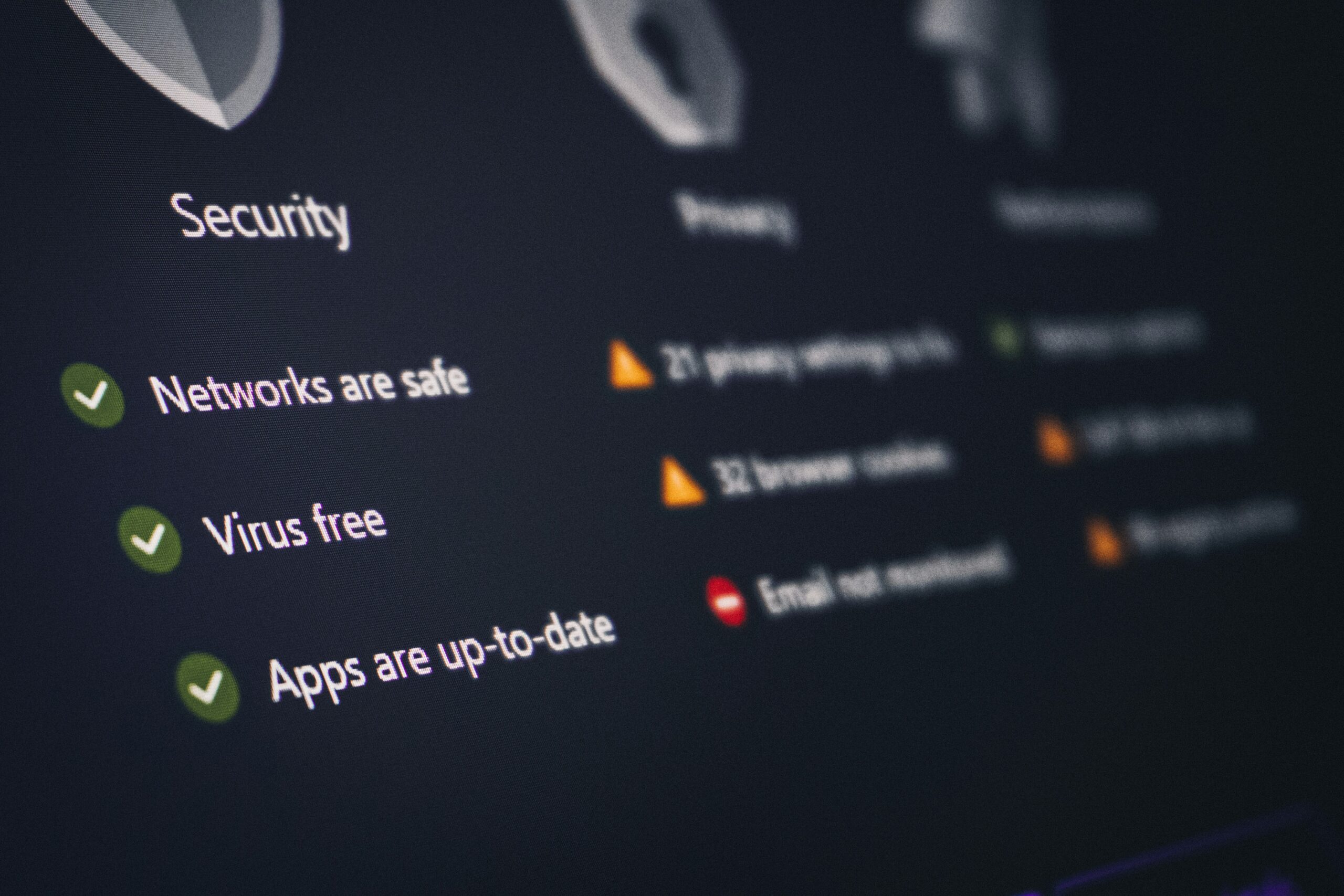
- Patch Regularly: Keep systems updated religiously. Think of patches as your caffeine fix—they revitalize security protocols.
- Train Employees: Social engineering remains the weak link. Conduct interactive simulations so everyone knows when something feels “phishy.”
- Use Endpoint Detection: Tools like CrowdStrike Falcon monitor endpoints 24/7, detecting anomalies in record time.
| Tool | Pros | Cons |
|---|---|---|
| CrowdStrike | AI-driven detection, fast response times | Expensive for SMBs |
| Norton Antivirus | User-friendly interface, affordable | Limited enterprise features |
Real-Life Examples That Prove Malware Is No Joke
In 2020, Twitter experienced its worst breach yet thanks to spear-phishing tactics aimed at employees. High-profile accounts—including Elon Musk’s—were hijacked to promote a Bitcoin scam. While embarrassing, it also underscored how vital human error prevention really is.
A second example: A hospital in Germany fell victim to ransomware, leading directly to patient deaths due to disrupted medical services. These stories drive home why acting preemptively beats reacting too late.

FAQ: Answering Your Burning Questions About Malware Threat Reports
Q: Are free malware scanners reliable?
A: They offer basic protection but rarely catch advanced threats. Invest in premium solutions whenever possible.
Q: How often should I review new malware threat reports?
A: At least quarterly, though monthly reviews provide greater peace of mind during high-risk periods.
Q: Can AI predict future malware trends?
A: Yes—with caveats. Predictive analytics helps anticipate patterns, but no algorithm catches everything.
Conclusion
Malware isn’t going anywhere anytime soon—but neither are smart defenders like YOU. By mastering malware threat reports, implementing robust safeguards, and learning from others’ mistakes, you’re already steps ahead. And remember: Staying safe online is less about magic shields and more about consistent effort.
Like keeping your old Tamagotchi alive (#nostalgia), protecting digital assets requires daily care. Stay sharp, stay informed, and don’t forget—you’ve got this!