Ever wondered who’s lurking behind your cybersecurity breaches? Spoiler: They’re not just hackers wearing hoodies in a basement anymore. Let’s dive into the profiles of today’s threat actors and uncover why they’re so dangerous.
In this post, we’ll explore what threat actor profiles are, how they’ve evolved, and most importantly—how you can defend against them. Expect practical advice, some brutal honesty, and maybe even a bit of nostalgia. Ready? Let’s go!
Table of Contents
Key Takeaways
- Cybercriminals come in various roles—from state-sponsored groups to lone wolves—and each has unique objectives.
- Threat actors target businesses through advanced tactics like phishing, ransomware, and social engineering.
- A proactive approach combining education, tools, and vigilance is essential for safeguarding data.
- Knowing your enemy isn’t just strategic—it’s survival.
How Have Threat Actors Changed Over Time?
Remember when malware was just annoying pop-ups on your PC? Those were simpler times. Fast forward to 2023, and cybercriminals have turned their chaos into an art form. According to McAfee, global cybercrime damages reached $8 trillion last year alone. Yikes.
Gone are the days when attacks were random; now, threat actors operate with precision, targeting specific industries or organizations. For example:
- State-Sponsored Hackers: Governments fund these experts to spy, disrupt, or steal intellectual property.
- Ransomware Gangs: Their business model? Encrypt your files, demand Bitcoin. Simple but devastatingly effective.
- Insiders: Sometimes, the biggest risk comes from within—an employee accidentally clicking malicious links or actively leaking info.
Who Are Today’s Top Threat Actor Profiles?

Optimist You: “If I understand them, I can outsmart them!”
Grumpy You: “Yeah, good luck staying ahead of people whose job is literally hacking.”
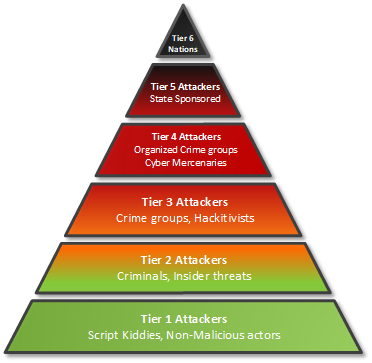
To beat the bad guys, you need to know who they are. Here are four common profiles:
1. Script Kiddies
The amateurs of the hacker world, using pre-built tools without much technical knowledge. Sure, they lack finesse—but don’t underestimate them. One misstep by you, and they’ll exploit it.
2. Organized Crime Rings
These cyber mobs treat hacking like any other enterprise. Ransomware-as-a-Service platforms let anyone rent malware, making entry-level criminals more dangerous than ever.
3. Nation-State Actors
Think James Bond villains, but real. Groups like Russia’s Fancy Bear specialize in espionage and sabotage. These players aren’t after money—they want power.
4. Insider Threats
Acknowledging this one hurts. Whether intentional or accidental, insiders often cause massive breaches because they already have access to sensitive systems.
How Can You Protect Your Business Against These Threats?
Listen up. Patch management. It sounds boring, but oh my gosh, you wouldn’t believe how many breaches happen simply because someone didn’t update their software. STOP being lazy about updates, okay?
Now that my rant’s out of the way, here are some proven strategies:
1. Employee Training
Don’t skimp on teaching your team! Teach them how to spot phishing emails, create strong passwords, and avoid suspicious downloads.
2. Multi-Layered Security
Combine firewalls, endpoint detection, and intrusion prevention systems into a cohesive strategy.
3. Regular Audits & Penetration Tests
Hire ethical hackers to find weaknesses before the bad guys do. Trust me; it’s worth the investment.
4. Data Encryption
Even if attackers get in, encryption ensures they can’t read your stolen data.
Pro Tip: Beware of DIY security solutions. Unless you’re an IT wizard, outsourcing might be smarter.
Real-World Scenarios of Threat Actor Exploits
Let’s look at two infamous cases:
Case Study #1: WannaCry Ransomware Attack
In 2017, WannaCry hit hospitals, banks, and governments worldwide, locking users out of critical files unless ransoms were paid. Shockingly, it exploited vulnerabilities Microsoft had already patched months earlier. Lesson learned? Update. EVERYTHING.
Case Study #2: SolarWinds Breach
Nation-state actors injected malware into SolarWinds’ Orion software, compromising thousands of U.S. companies and government agencies. This attack highlights the importance of vetting third-party vendors rigorously.

Frequently Asked Questions (FAQs)
What Exactly Is a Threat Actor Profile?
A detailed breakdown of a potential attacker’s behavior, motivations, skills, and likely methods used during attacks.
Is AI Being Used by Cybercriminals?
Unfortunately, yes. AI helps automate attacks, crack passwords faster, and adapt malware based on system defenses.
Are Small Businesses Safe from Advanced Threats?
Nope. Smaller targets are appealing due to weaker security measures. Don’t think size matters when it comes to cybersecurity!
Should I Hire a Dedicated Security Team?
If budget allows, absolutely. Otherwise, consider managed service providers specializing in cybersecurity.
Final Thoughts
We live in a digital jungle where understanding predator behavior keeps us safer. By learning about threat actor profiles, implementing robust defenses, and keeping employees informed, you significantly reduce risks.
And remember…
Like floppy disks in the ’90s,
Your data needs protection too.
Stay sharp, stay secure.


